How to Use Saved Passwords Everywhere
Some web sites and applications prevent users from using previously saved credentials. There a very few legitimate reasons to do so. In the vast majority of cases, such measures just patronize users, often those people that actually keep up the service with their financial support. But it is actually quite simple to bypass such paranoid settings.
What Is Wrong With Saving Passwords?
Nothing, if you do it right. If you have a password cache that is protected by a master password, it is reasonably safe to use, when you do not leave your computer unattended. In practice that means that you should always lock the screen, when you leave your computer.
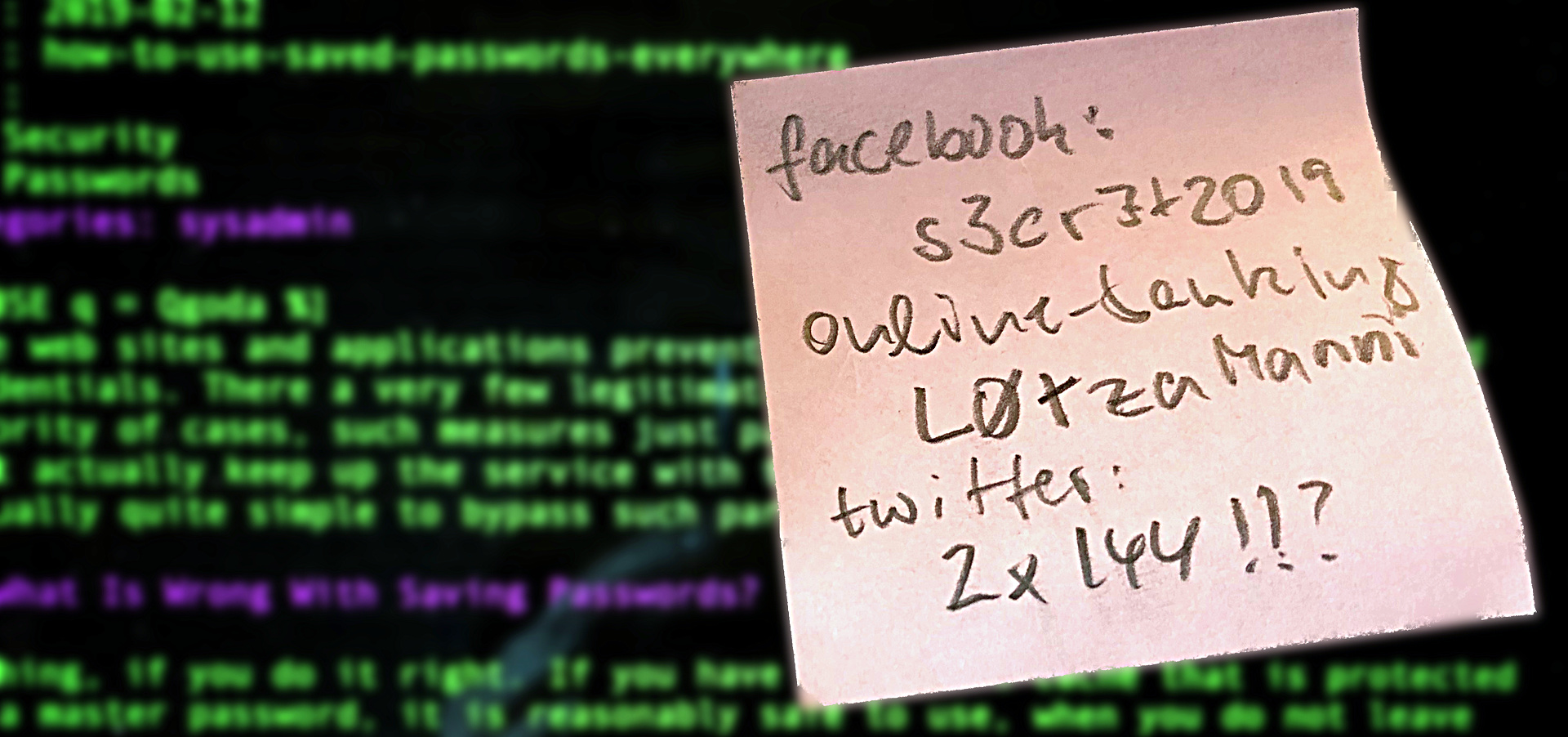
Preventing the usage of saved passwords, like many other well-meant but patronizing password policies will often result in less security. If you cannot save your password, or if you are forced to follow paranoid rules, many people resort to completely unsafe ideas like post-it stickers on the monitor.
Why Circumventing These Measures?
Well, I don't want to be patronized. And there are some particularly annoyoing cases.
Recently, I had to do a training for employees of a customer of mine. That customer uses a Cisco VPN appliance and I am forced to use the Mac OS X VPN client to connect to it. The password is a generated one, I cannot change it, and the VPN connection breaks down after at most 30 minutes.
Short of any other method, I have the password saved in a file. But the day before the training, I wondered how could I enter the password in the VPN client, airplaying my screen to the Apple TV? Fortunately, there is a Command Line tool pbcopy for Mac OS X that copies a text to the clipboard so that you can paste it with CMD-V resp. CTRL-V into forms. And if it is a password field with echoing turned off, it is not visible. So I ended up writing a little shell script pwcopy that is installed in ~/bin, which is in my $PATH:
#! /bin/sh
# Use "xclip -i" on linux.
PBCOPY=${PBCOPY:-pbcopy}
if test "x$1" = "x"; then
exec 1>&2
echo "Usage: $0 [IDENTIFIER]"
exit 1
fi
case $1 in
xyz)
pass=n0t5053cr3t
;;
*)
exec 1>&2
echo "$0: error: unknown password IDENTIFIER '$1'"
exit 1
esac
echo "$pass" | perl -p -e 's/\n//' | $PBCOPYYou call it like pwcopy xyz and the password for the service "xyz" is copied to the clipboard.
On Linux you have to install the package xclip and run the script with the environment variable PBCOPY set to xclip -i or rather just change the script. You have to edit the script anyway to set passwords for more services.
Needless to say that it is probably a good idea to make the script readable and executable only for yourself.
Isn't That Unsafe?
Yes and no, decide yourself. If for whatever reason you cannot remember your password, what will you do? You will save it somewhere. On a file in your computer or under your pillow. If you agree that saving it on your computer is actually reasonable safe, when you protect your computer, then the script is safe because it is just a very comfortable way of saving such passwords. Compared to a file ~/passwords.txt it has the additional benefit that you can use the saved information, even when somebody is looking over your shoulder.
If you think that this is a lame argument, well, then make the script readable and executable only for root or encrypt it with gpg and decrypt and run it on the fly. But keep in mind that stealing other people's passwords is in practice more a financial than a technical problem. Bruce Schneier has described seven well-known types of cryptanalysis:
- Ciphertext-only attack
- Known-plaintext attack
- Chosen-plaintext attack
- Adaptive-chosen-plaintext attack
- Chosen-ciphertext attack
- Chosen-key attack
- Rubber-hose cryptanalysis
He elaborates on the rubber-hose cryptanalsis as follows:
The cryptanalyst threatens, blackmails, or tortures someone until they give him the key. Bribery is sometimes referred to as a purchase-key-attack. These are all very powerful attacks and often the best way to break an algorithm.1
Put into simple words, rubber-hose cryptanalysts will break into your home and hit you in the face with their rubber-hose until you not only give them all of your cautiously stored passwords but also pay their taxi home.
Encryption technology has made rapid progress in the last decades but the traditional, conventional ways of stealing other people's secrets and assets are essentially the same as in the stone age, and still cheap and efficient.
- Schneier, Bruce (New York, Chichester, Brisbane, Toronto, Singapore 1997). Applied Cryptography Second Edition: protocols, algorithm, and source code in C, p. 5-7. ISBN 0-471-12845-7↩
Leave a comment
Giving your email address is optional. But please keep in mind that you cannot get a notification about a response without a valid email address. The address will not be displayed with the comment!